Sponsored by Fortinet
Sponsored by Illusive Networks
Utilizing Deception Technology To Protect ATM Networks
Sponsored by Flexera Software
The Complexities of Vulnerability & Patch Management
Sponsored by Simility
The Fraud Challenges in Mobile Financial Services
Sponsored by Simility
Reducing Fraud In Digital Banking
Sponsored by Simility
The Device Fingerprinting Evolution
Sponsored by Illusive Networks
Three Use Cases for Deception Technology in Healthcare
Sponsored by Illusive Networks
Three Use Cases for Deception Technology in Financial Services
Sponsored by Illusive Networks
A Deception Approach to Protecting ATM Networks
Sponsored by Illusive Networks
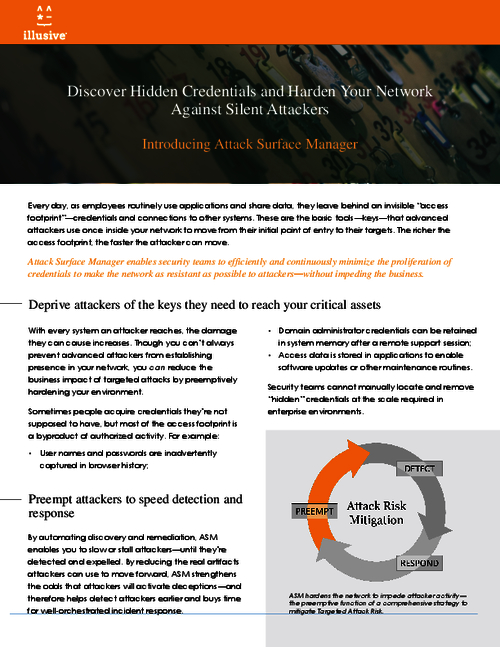
Discover Hidden Credentials and Harden Your Network Against Silent Attackers
Sponsored by Illusive Networks
How Can Deception Technology Help The Healthcare Industry?
Sponsored by Sift Science
Stopping Content Abuse Before It Happens
Sponsored by Sift Science
The Future of Fraud Fighting
Sponsored by Sift Science
E-Commerce's Guide To Stopping Content Abuse Before It Happens
Sponsored by Sift Science