Sponsored by Barracuda
Sponsored by Avast Business
The Security Impact of Digital Transformation
Sponsored by Synopsys
CISO Research Identifies 4 Distinct Approaches to the Role
Sponsored by Synopsys
The CISO's Terrible, Horrible, No Good, Very Bad Day
Sponsored by Synopsys
The CISO's Ultimate Guide to Securing Applications
Sponsored by Splunk
In The Mirror Land of The Data (German Language)
Sponsored by Splunk
The 5 Basic DevOps Methods (German Language)
Sponsored by Splunk
The Seven Core Features of Analytics-Based SIEM Solutions (German Language)
Sponsored by Splunk
Modernize Your IT Monitoring with Predictive Analytics (German Language)
Sponsored by Dell EMC solutions with Intel
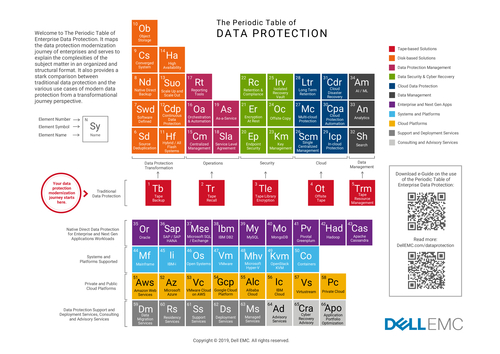
The Periodic Table of Data Protection
Sponsored by Dell EMC solutions with Intel
Data Protection Protect Your Data Capital From The Edge of the Core to the Cloud
Sponsored by OneTrust
Information Security Management System (ISMS) Industry Standards: A Help Guide
Sponsored by BMC
Aligning the Business and Cloud Operations
Sponsored by BMC