Sponsored by Illusive Networks
Sponsored by Illusive Networks
The Role of Deception Technology in M&A
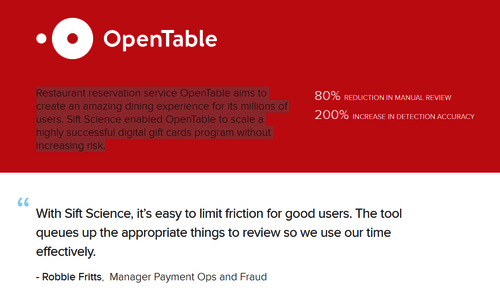
Sponsored by Sift Science
Case Study: Enhancing User Experience While Mitigating Risk
Sponsored by Digital Shadows
Top Cybercrime Threats to Financial Institutions in 2018
Sponsored by Digital Shadows
Bank Employee Offering Insider Information
Sponsored by Lastline
A New Look at Email Security: How to Improve Detection of Malicious Payloads
Sponsored by WhiteHat Security
Application Security: Why the Whole Company Needs to be on Board
Sponsored by LogMeIn
Why Your Organization Needs Better Endpoint Management
Sponsored by LogMeIn
Conquering Complexity in Endpoint Management
Sponsored by Wombat
2018 State of The Phish Report ®
Sponsored by Illusive Networks
Utilizing Deception Technology To Protect ATM Networks
Sponsored by FireEye