Sponsored by Tenable
Sponsored by Tenable
Using Security Metrics to Drive Action
Sponsored by Level 3
Why Are Retailers So Vulnerable to Cyber Attacks?
Sponsored by BioCatch
Is the Promise of Behavioral Biometrics Worth the Investment?
Sponsored by Akamai
Top 10 Things to Look for in a Cloud Security Solution Provider
Sponsored by NSFOCUS
The Intelligent Hybrid Security Approach
Sponsored by Bottomline
Ignoring Risks from Same-day ACH Will Cost You Big
Sponsored by Fox-IT
Lessons Learned from Studying Cybercrime
Sponsored by Level 3
Is Your Organization Prepared for Today's Sophisticated Cyber Threats?
Sponsored by Level 3
2017 Cyber Threat Checklist: Are You Prepared?
Sponsored by PhishMe
Why Can't We Solve Phishing?
Sponsored by Carbon Black
Streaming Prevention: Breakthrough Prevention That Stops All Forms of Attacks
Sponsored by Carbon Black
Ransomware on the Rise: An Enterprise Guide to Preventing Ransomware Attacks
Sponsored by Carbon Black
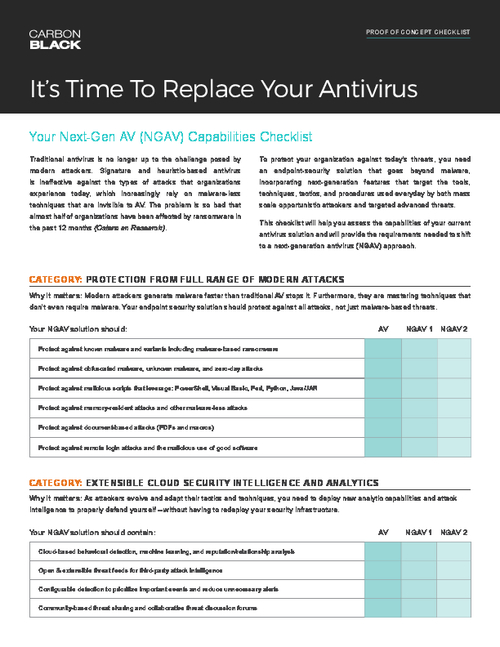
Out with the Old, In with the New: Next Generation Antivirus
Sponsored by Carbon Black