Sponsored by Moka5
Sponsored by ThreatMetrix
Context-Based Authentication & Fraud Protection for Mobile Devices
Sponsored by Trusteer
Mobility on Hold: Get Back on Track with Mobile Risk Mitigation
Sponsored by Webroot
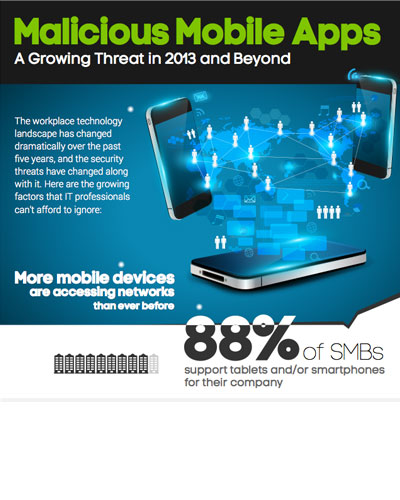
Malicious Mobile Apps: A Growing Threat in 2013 and Beyond
Sponsored by Webroot
Mobile Browsing - Is Your Company at Risk?
Sponsored by HP
Top Three Mobile Application Threats
Sponsored by iovation
Fighting Mobile Fraud - Protecting Businesses and Consumers From Cybercrime
Sponsored by Dell SecureWorks
Six Key Guidelines for Securing Mobile Banking Apps
Sponsored by Dell SecureWorks
Making Mobility Matter in Healthcare Data Security
Sponsored by i2 Group
5 Emerging Mobile Cyber Crime Trends
Sponsored by Experian
Data Privacy and Trust in the Mobile World
Sponsored by Good Technology
Case Study - Secure Data on Mobile Devices
Sponsored by Good Technology
Data Loss Prevention: When Mobile Device Management Isn't Enough
Sponsored by Good Technology