Sponsored by LogMeIn
Sponsored by Illusive Networks
A Deception Approach to Protecting ATM Networks
Sponsored by Illusive Networks
Three Use Cases for Deception Technology in Healthcare
Sponsored by Akamai
5 Steps To Starting Your Cloud Perimeter Journey
Sponsored by Tata Communicatiions
The State of Organizations' Security Posture as of Q1 2018
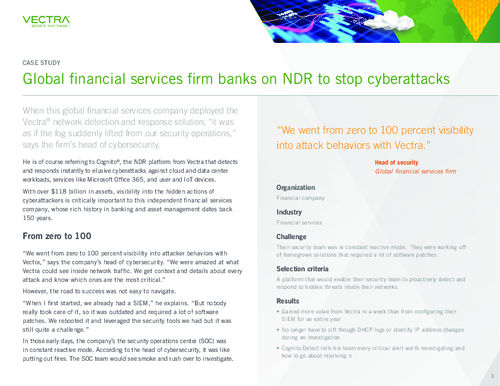
Sponsored by Vectra