Cybercrime , Fraud Management & Cybercrime , Fraud Risk Management
'Scam-as-a-Service' Scheme Spreads
Researchers: 40 Gangs Used Phony Classified Ads to Launch Phishing Schemes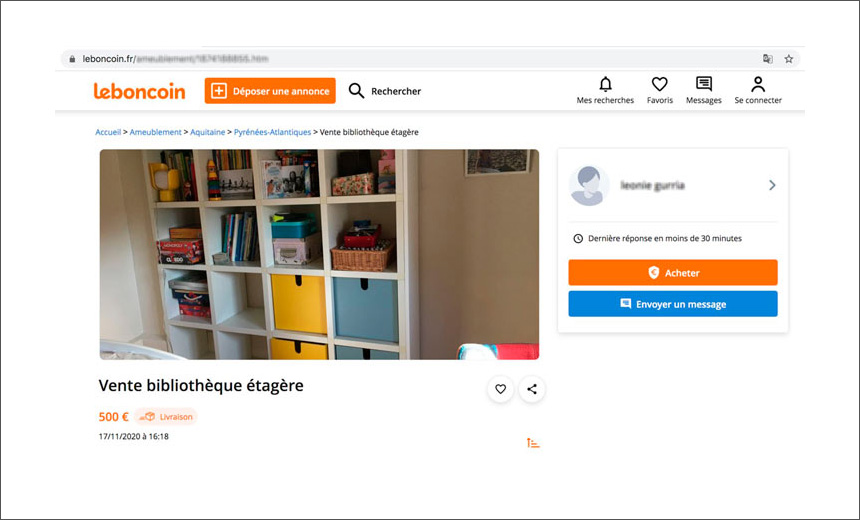
A Russian-speaking "scam-as-a-service" operation dubbed "Classiscam" is expanding globally, with 40 interconnected gangs in about a dozen countries using fake product advertisements to launch phishing schemes, the security firm Group-IB reports.
The fraudsters are posting fake online classified advertisements for products to dupe interested buyers into visiting phishing pages, where their personal and payment data is harvested, according to Group-IB.
Although the operation started in Russia two years ago, by early 2020, it had expanded to include 40 subgroups that have focused on targets in the U.S. and Europe, the new research report says.
Brands spoofed by the cybercriminal gang include French marketplace Leboncoin, the Polish online brand Allegro, the Czech website Sbazar and Romania's FAN Courier site. The report also notes the group has expanded its operations in the U.S. and Bulgaria by mimicking FedEx and DHL Express.
"More than 20 large groups are leveraging the scheme, and currently operate in Bulgaria, the Czech Republic, France, Poland, Romania, the U.S, and post-Soviet Union countries, while 20 more groups work in Russia," according to the Group-IB report. "These 40 groups altogether made at least $6.5 million in 2020."
Classiscam
The Group-IB report notes the criminal group scaled up its operations in 2020 in response to the boom in online shopping during the COVID-19 pandemic.
A scheme typically starts with fake advertisements placed on popular online marketplaces and classified ad websites for products, such as cameras, game consoles, laptops and smartphones, offered at low prices, according to the report.
"When the buyer contacts the seller, they are lured into continuing the conversation through a third-party messenger, such as WhatsApp," Group-IB says. "To be more persuasive, the scammers use local phone numbers when speaking with their victims. Such services can be obtained in the underground."
When the interested customers ask the fraudsters, who are disguised as the sellers, to send the shipping details, the victims are directed to phishing landing pages that mimic courier service websites or marketplaces with a payment form, the report notes.
"As a result, the fraudster obtains payment data or withdraws money through a fake merchant website," according to the analysts.
The Group-IB report estimates that each of the 40 groups make a total profit of $522,000 per month.
Telegram Bots
The hackers have set up several Telegram chatbots for automated management and expansion of the scheme, the report notes. These bots are designed to provide scammers with ready-to-use pages mimicking popular classified advertising, marketplace and phishing URLs.
"Classiscam chatbots, where fake pages are generated and profits are reported, are not completely autonomous. They require ongoing technical support and moderation," says Dmitriy Tiunkin, head of the digital risk protection department at Group-IB Europe. "The admins are on top of the Classiscam pyramid. They fund and moderate the chats, recruit new members, register new accounts and allocate the profits among group members. Sometimes they hire third-party developers to create the chatbots. They also buy new domains. … In most cases they use content delivery network infrastructure from popular providers to hide their real hosting."
Group-IB researchers identified 10 Telegram bots being used by hackers to generate scam pages for brands from Bulgaria, the Czech Republic, France, Poland and Romania. "For each brand and country, scammers write scripts that help newbie workers log into foreign sites and communicate with victims in the local language," the report notes.
By the end of 2020, Group-IB says, the chatbots had more than 5,000 scammers registered to use its services.
Classiscam Operators
Group-IB notes each of the 40 criminal groups has put in place three role-players to help move the operation along.
Admins, or "topic starters," recruit new members, create scam pages, register new accounts and provide assistance when a bank blocks the recipient's card or the transaction. "Workers" communicate with victims and send them the phishing URLs. And "callers" pose as tech support specialists.
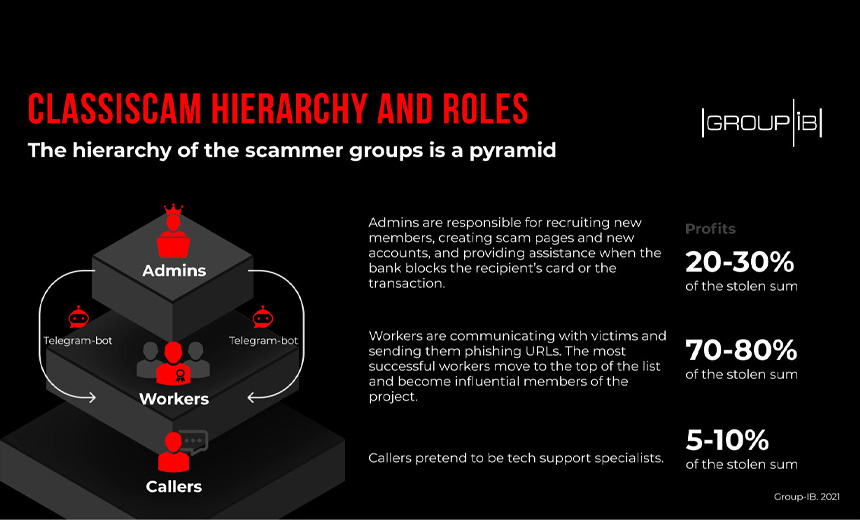
"Based on payment statistics, the most successful workers move to the top of the list and become influential members of the project," the report notes. "By doing so, they gain access to VIP options in the chats and can work on European marketplaces, which offer a higher income and involve less risks for Russian-speaking scammers."