Breach Notification , Business Continuity Management / Disaster Recovery , COVID-19
Maryland Health Dept. Systems Still Affected by Incident
Employees Asked Not to Use State-Issued Computers While Officials Investigate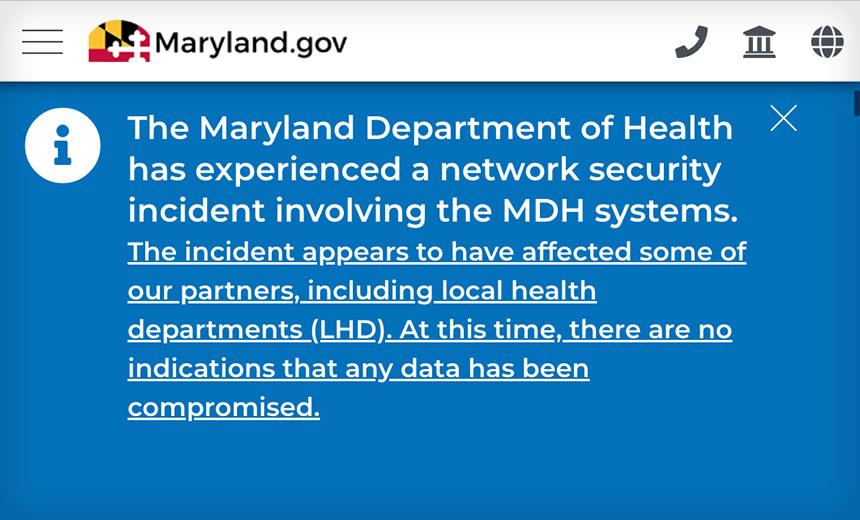
Maryland officials are asking employees not to use state-issued computers as it continues to deal with a network security incident detected at the state's Department of Health over the weekend, which caused authorities to take certain systems, as well as the department's public website, offline.
See Also: Ransomware Response Essential: Fixing Initial Access Vector
As of Monday night, the department's website was operational again, but on Tuesday, some other systems remained offline as the state's IT experts and law enforcement agencies investigate, a Maryland Department of Health spokesman says.
"The Maryland Department of Information Technology, the Maryland Department of Health, and the Maryland Department of Emergency Management are working closely with federal and state law enforcement partners to address and gather information about the network security incident that was discovered this past weekend," he says in a statement provided to Information Security Media Group.
"As previously stated, we have taken certain systems down out of an abundance of caution. Similarly, we have asked employees to not use state-issued computers," he says.
The spokesman says there is no evidence at this time that any data has been compromised.
"Another top priority is COVID data reporting, which will resume at the earliest opportunity. The investigation is ongoing," he says.
Rerouted Website Traffic
While the Health Department's website was offline over the weekend, visitors were automatically redirected to the state's main government website.
But services such applying for Medicaid and resources for accessing nursing home and other data were unavailable.
On Tuesday, a message on Maryland's website informed visitors that the Health Department was experiencing a "server outage" and that COVID-19 surveillance data would be updated as soon as possible.
The Health Department's website also advised visitors that its network security incident "appears to have affected some of our partners, including local health departments."
Ransomware Attack?
The Maryland Department of Health did not immediately respond to ISMG's inquiries about the type of cybersecurity incident that occurred and the extent of how other local health departments and partners were affected.
"Statistically speaking, this is most likely to be yet another ransomware incident and it seems to have impacted multiple services," Brett Callow, a threat analyst at security vendor Emsisoft, tells ISMG.
Other Incidents
The Maryland incident is the latest in a rash of cyberattacks and other security incidents over the past year or so affecting healthcare sector organizations, including public health departments and related entities, in the U.S. and elsewhere.
For instance, in the U.S., Alaska's Department of Health and Social Services in May experienced a "malware attack" that forced the department to take down its public website, a background check system, the state's vital records system, and the state's system for schools to report vaccine data to public health for several days.
The Alaska incident was reported to federal officials in September as a HIPAA breach affecting the protected health information of 500,000 individuals.
Outside the U.S., Ireland's health system in May revealed that it had been the victim of a ransomware attack.
"With the pandemic, more significant motives to pursue cybercrime through such avenues as ransomware can evolve because of the importance given to protecting critical data and information, especially if vaccine and personally identifiable information are part of the data qualities," says Stanley Mierzwa, director of the Center for Cybersecurity at Kean University in Union, New Jersey.
"Cyberthreat actors recognize the premium given to such valuable information."
Mierzwa suggests that greater research knowledge in studying such cybercriminal activities can be a path for understanding the psychology of threat actors, and ultimately help defenders put better cyber defenses in place in organizations.
Taking Action
In the meantime, organizations, including healthcare sector entities, should take many proactive steps to help prepare for the possibility of a ransomware or other serious cyberattack, he says.
Mierzwa suggests a subset of high-level tasks including:
- Creating a ransomware policy or, at a minimum, a policy brief, that states the executive summary of the problem for leadership, as well as the recommended steps to be taken;
- Awareness activities with executive leadership and board members on the potential for ransomware and how it is envisioned or agreed to be handled;
- Clear lines of communication and response handling expectations with an organization's insurance broker on cybercriminal incidents such as ransomware.