Fraud Management & Cybercrime , Governance & Risk Management
DDoS Attacks Against Banks Increasing
Financial Institutions Seek New Ways to Mitigate the Risks
Three years after leading U.S. banking institutions were targeted by waves of distributed denial-of-service attacks waged against them by the hacktivist group known as Izz ad-Din al-Qassam Cyber Fighters, DDoS attacks have continued to grow in number and magnitude.
See Also: Small Business. Large security risks.
And while banking institutions have made improvements in their abilities to mitigate the effects of DDoS strikes against them, institutions are still struggling to keep up.
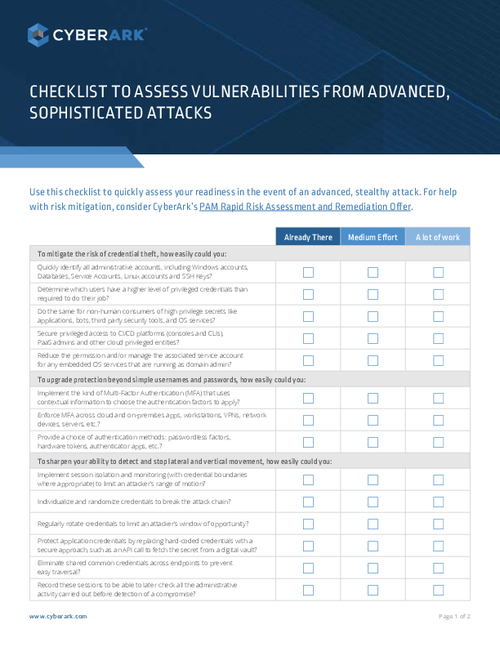
Some 25 percent of banks rank insufficient technical tools as a leading deficiency in their fight against DDoS attacks, according to a new survey of 300 financial institutions conducted by Information Security Media Group and sponsored by DDoS mitigation firm Neustar. Another 25 percent rank insufficient staff as a leading hindrance, the survey shows.
But Joseph Loveless, a member of Neustar's product management team who analyzed the results for a webinar, says banks and credit unions are detecting DDoS attacks much sooner than they were two to three years ago. Still, the potential damage is greater.
Loveless says today's DDoS attacks are increasingly waged as modes of distraction to mask fraud that's taking place in the background.
"The DDoS attack is laid down as a distraction to consume resources, to consume IT attention, while actually different activity is going on, whether it be the insertion of malware, or an open breach to steal financial assets," Loveless says.
Banking institutions have the potential to lose approximately $100,000 per hour, because of downtime-related costs and possible fraud, during a DDoS attack, Loveless says. With that much at stake, banks must continue to improve their detection and response times, he adds.
"Today, in the [ISMG] study that we see here, organizations are detecting [DDoS attacks] in less than an hour," Loveless says. "That means sharper skills; it means much stronger defenses; it means the incorporation of third-party defenders who are constantly looking and screening traffic; it means always-on configurations, where traffic is constantly moving through mitigation to make sure that no DDoS is actually occurring."
Neustar reported in its 2015 DDoS Attacks and Protection Report, published in April, that 88 percent of financial-services respondents say they detect attacks in less than two hours, and 72 percent say they respond to attacks in less than two hours. "This is a marked improvement over responses in Neustar's 2014 'The Danger Deepens DDoS Attacks and Impact Report," Loveless says.
Technical Challenges?
The problem, however, is that banking institutions continue to struggle to keep up with the technological and staffing investments needed to mitigate ongoing DDoS risks.
Online security firm Akamai notes that a recent survey of its customers showed 42 percent of respondents have no plans in place to combat the escalation of DDoS attacks. That's why more businesses are considering moving DDoS mitigation and online security to the cloud, Akamai contends.
Roland Dobbins, principal engineer at DDoS mitigation firm Arbor Networks, says banking institutions now have a better understanding of the risks of fraud and intellectual property theft during a DDoS attack. DDoS is not just seen as a nuisance anymore.
As a result, banks today are no longer relying solely on their own IT teams to mitigate the threat of DDoS outage, he says. Instead, many have "implemented and tested commercial DDoS mitigation services in order to defend against DDoS attacks that exceed their provisioned Internet bandwidth."
They also are paying much more attention to their Internet-facing traffic to detect DDoS attacks sooner, he adds.
As threat intelligence sharing and outsourced security for DDoS mitigation increases, banks and credit unions are much less likely to be taken down by a DDoS attack than they were three years ago, experts say. But financial institutions have to remain constantly vigilant to keep up with emerging threats.
Attacks Increasing in Size and Frequency
In December 2012, during the al-Qassam Cyber Fighters' DDoS attacks, Mike Smith of Internet platform provider Akamai Technologies told ISMG that banks were being targeted with attacks that averaged between 60 and 65 gigabytes per second. At the time, those were among the largest DDoS attacks the industry had tracked.
Today, DDoS attacks tracked by banks are coming in at anywhere from 196 gigabytes per second to just less than 300 gigabytes per second, Loveless says.
What's more, the attacks are being waged more frequently.
In the ISMG survey, 56 percent of banks say they've seen an uptick in the number of DDoS attacks waged against them in the last year, and 60 percent say the attacks are larger than they were a year ago.
DDoS for Cybercrime
Knowing the actors who wage these attacks is becoming more of a priority as part of the effort to combat fraud. ISMG's survey confirms that banks believe cybercrime is the driving force for most DDoS strikes.
According to the survey, most institutions believe DDoS attacks are being waged by cyber criminals and cyber vandals, rather than hacktivists or nation-states, as they were three years ago.
The purpose of the attacks waged by al-Qassam Cyber Fighters in 2012 and 2013 against U.S. apparently was not to perpetrate fraud or to extort funds, but merely to take down institutions' online presence. The group claimed the attacks were waged because of outrage over a YouTube movie trailer deemed offensive to Islam, and many concluded that Iran was behind the campaign.
Banking institutions say they believe only 16 percent of the DDoS attacks are now waged by hacktivists, and only 10 percent are waged by nation-states (see Ex-FBI Official on Why Attribution Matters).
Financial fraud expert and Gartner analyst Avivah Litan says the financial damage posed by DDoS is much more severe than most industry experts and banking institutions acknowledge.
Litan says DDoS attacks are increasingly being used to wage cyber-extortion attacks, which aim to blackmail banks into paying out high ransoms to avoid having their sites taken down and intellectual property published in the underground.
"Cyber-extortion is probably the hottest trend of 2015," she says. "They'll get malware on the network, extract information from files and then threaten to publish it. Then they wage a denial-of-service attack against the bank. So, this has been going on for a while, and banks are paying out."
Targeted institutions are paying ransoms of $5 for every $100 worth of damage they could suffer if the extracted data were published, Litan says. "They feel it's better to pay out than suffer the damage," and - without naming names - she says many big-name institutions have been affected.