Data Loss Prevention (DLP) , Fraud Management & Cybercrime , Governance & Risk Management
Former Employee Kept Accessing Engineering Firm's Servers
Cybercrime Prevention: Block Ex-Employees' Access, Prohibit Credential Sharing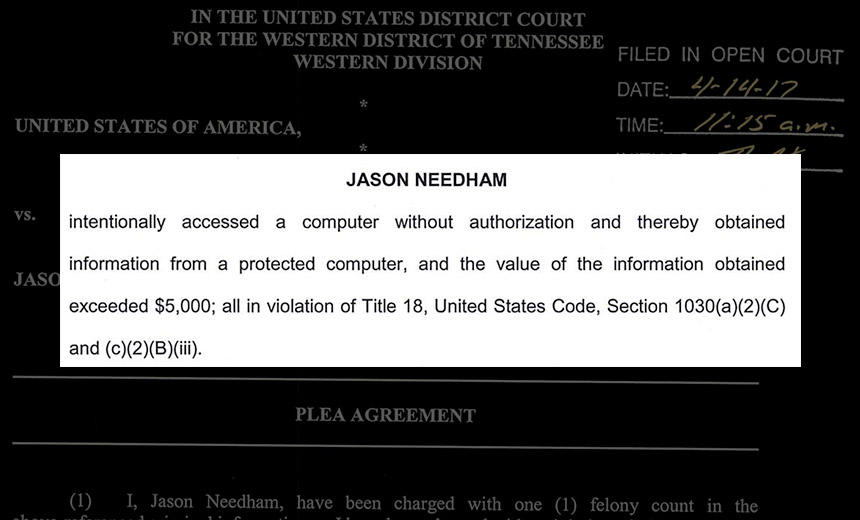
Businesses that fail to block former employees' server access or spot any unauthorized access to the corporate network are asking for trouble.
Of course, the vast majority of ex-employees will behave scrupulously. But why leave such matters to chance?
Witness a case involving Jason Needham, 45, the co-owner of HNA Engineering, a small engineering firm based in Arlington, Tennessee. He's admitted to snooping on his former employer - turned competitor - for two years.
On April 14, according to court documents, Needham pleaded guilty before U.S. District Judge John T. Fowlkes Jr. to intentionally accessing his former employer's servers, without authorization, after he'd left the company - from May 2014 through March 24, 2016. As part of that plea, Needham admitted that he'd obtained information worth more than $5,000 in violation of the Computer Fraud and Abuse Act - aka 18 U.S.C. 1030 - which is a felony.
"As part of his guilty plea, Needham admitted that, over a nearly two-year period, he repeatedly accessed the servers of Allen & Hoshall, his former employer, to download digitally rendered engineering schematics and more than 100 PDF documents containing project proposals and budgetary documents," accroding to the Department of Justice.
Needham also "admitted to accessing, on hundreds of occasions, the email account of a former colleague at Allen & Hoshall, which provided Needham access to the firm's marketing plans, project proposals, company fee structures and the rotating account credentials for the company's internal document-sharing system," the Justice Department says.
Allen & Hoshall provides engineering, architecture, planning and consulting services. The Justice Department said the information viewed, downloaded or copied by Needham was estimated to be worth $425,000.
As part of his plea deal, Needham agreed to make restitution of $127,500 to his former employer, cover $8,900 in legal fees and $3,400 in equipment and software replacement, as well as to pay for 12 months of identity theft monitoring "for each of the ... individuals whose email accounts [he] compromised," according to court documents.
Needham is due to be sentenced July 14. He faces up to five years in prison and a $250,000 fine, followed by up to one year of supervised release.
In the meantime, he's been released on a personal recognizance bond, meaning he's made a written promise to attend future court appearances, submit to being supervised by a pretrial agency, and promise to not break any federal, state or local law while on release.
Dump Ex-Employees Off Network Resources
What's not clear is how Needham gained access to his former Allen & Hoshall co-worker's email account. I couldn't immediately reach officials at the firm for comment.
Justice Department spokesman Peter Carr, meanwhile, tells me he cannot currently offer additional details. "We are limited to the information included in the public court documents," he says, adding that more details may come to light at sentencing.
But the obvious explanation would be that at some point before Needham departed, the other Allen & Hoshall employee either left their access credentials in a visible location - sticky note on the monitor - or else shared them directly with Needham.
Of course, organizations should have security policies in place that prohibit such behavior, as well as automated checks that ensure compliance. Too often, however, they fail to put such safeguards in place.
"We regularly come across cases where former employees have abused access to the companies' systems," Dublin-based information security consultant Brian Honan, who serves as a cybersecurity adviser to adviser to the EU's law enforcement intelligence agency - Europol - tells me. "Many companies leave ex-employee's accounts active in case they need to access something within the account, rather than take the time to manage the leaving of the employee in a more secure manner."
Password Hygiene
There are numerous steps companies can take to better secure access to systems. One example: to avoid having employees write things down, issue them with a password manager instead for their PCs and smartphones. Also ensure they're using long, complex and unique passwords - these are easy to generate and store with a password manager - and tell them to keep them secret.
While many security experts now no longer recommend forcing passwords to expire, doing so may have led to an immediate loss of Needham's access to his former employer's server (see Why Are We *Still* So Stupid About Passwords?).
Protecting systems using two-factor authentication, meanwhile, means that organizations could potentially expire an ex-employee's token, thus further blocking access.
Social Engineering Attackers Within
Of course, engineering firms aren't the only ones at risk from employees sharing or inadvertently divulging their access credentials, for example via phishing attacks that trick them with real-looking but fake log-in pages.
Another threat, however, comes from insiders with potentially malicious intentions. Regardless of what you think of former National Security Agency contractor Edward Snowden's decision to leak documents relating to U.S. mass surveillance programs, for example, he evidently relied on his fellow NSA employees' access credentials to do so.
Based on a February 2014 NSA memo signed by Ethan Bauman, the NSA's director of legislative affairs that was obtained by NBC News, "an NSA civilian employee, an active duty military member, and a contractor" were also implicated in the leaks.
The civilian employee, for example, resigned over allegations that he'd inadvertently shared access credentials with Snowden by entering his public key infrastructure password into Snowden's system, at his request, but in violation of NSA security rules. "Unbeknownst to the civilian, Mr. Snowden was able to capture the password, allowing him even greater access to classified information," the memo states.
This piece has been updated with comment from Peter Carr and Brian Honan, and to mention two-factor authentication.











